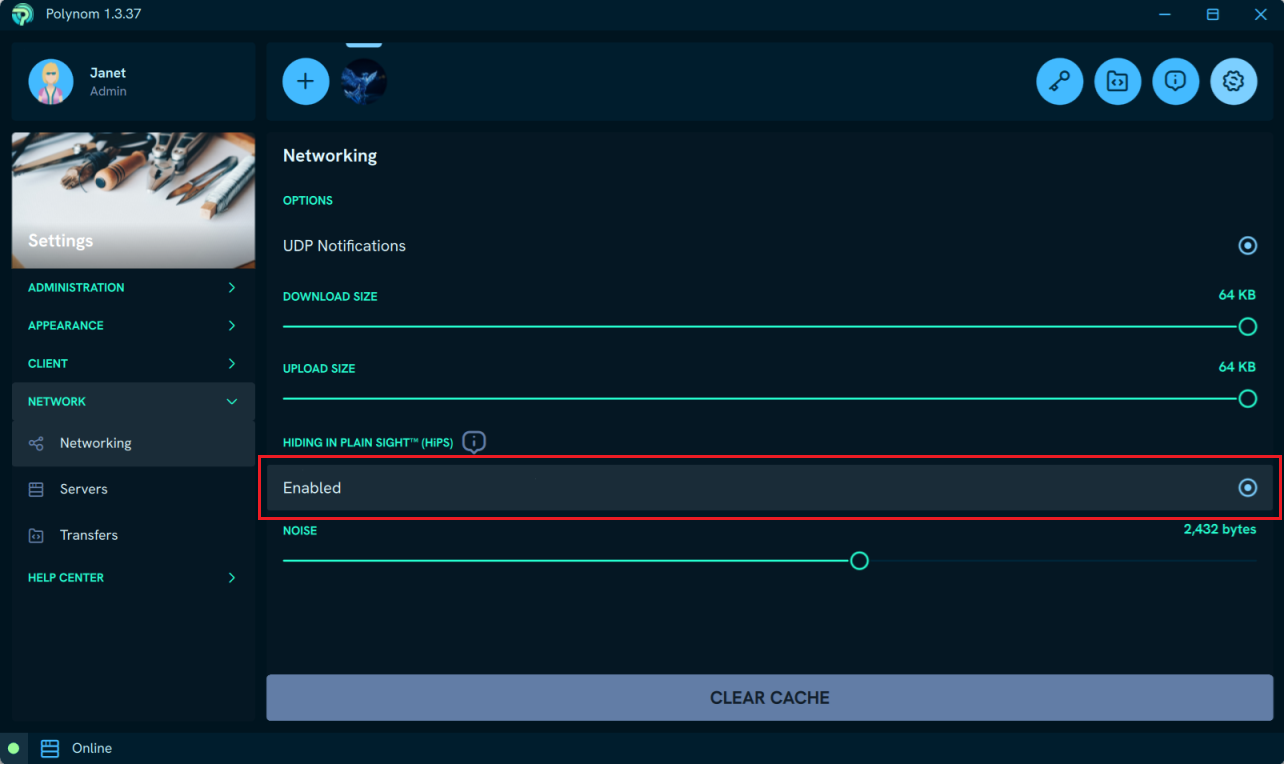
¶ Hiding-in-Plain-Sight™
Hiding-in-Plain-Sight™ (HIPS) technology allows Polynom to operate securely on compromised networks, hostile servers, and in regions where encrypted communications may be blocked or surveilled, at a level equivalent to a Type 1 Cryptographic device.
Polynom achieves this through several techniques designed to disguise its traffic and make it resistant to detection and blocking.
¶ Traffic obfuscation
Polynom adds random noise to the lengths of requests and responses, making it impossible to write firewall rules based on fixed message lengths. Polynom also varies how its traffic is presented at the byte level, masquerading as different Internet standard byte patterns to resist deep packet inspection.
¶ Control messages
The only unencrypted packets Polynom uses are control messages. These use random bytes and modulus math to transfer meaning across the network, ensuring that even an intercepted control message reveals nothing about its content or intent.
¶ Post-Quantum encryption
All communication is further protected by AES-256-GCM, ML-KEM-1024, and ML-DSA-87, making Polynom one of the most secure communications platforms available.
For further reading, see: Post-Quantum Cryptography and How the Great Firewall of China Detects and Blocks Fully Encrypted Traffic.
For further reading on Polynom's encryption standards, see Polynom's Encryption and Social Encryption.